Pharma & Medical Products
PharmaLogic Holdings Corp. team
Plants & Facilities
PharmaLogic Opens Radiopharmaceutical Production FacilityPharmaLogic Opens Radiopharmaceutical Production Facility
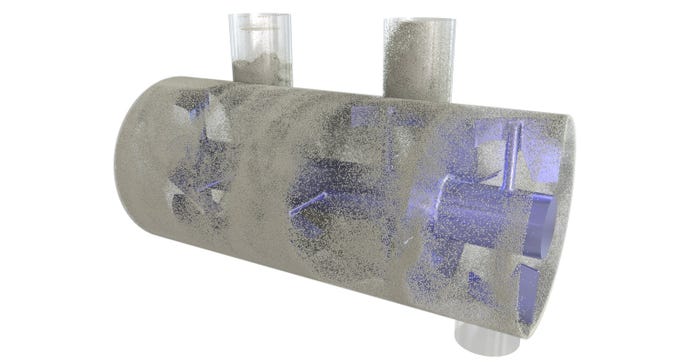
The company opened its new radiopharmaceutical production and research facility in Cincinnati.
Sign up for the Powder & Bulk Solids Weekly newsletter.































.jpg?width=100&auto=webp&quality=80&disable=upscale)







